Active malware campaign uses thousands of WordPress sites to infect visitors
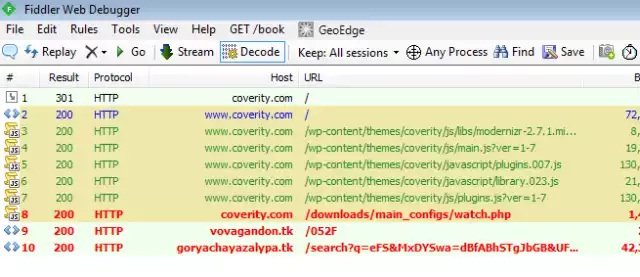
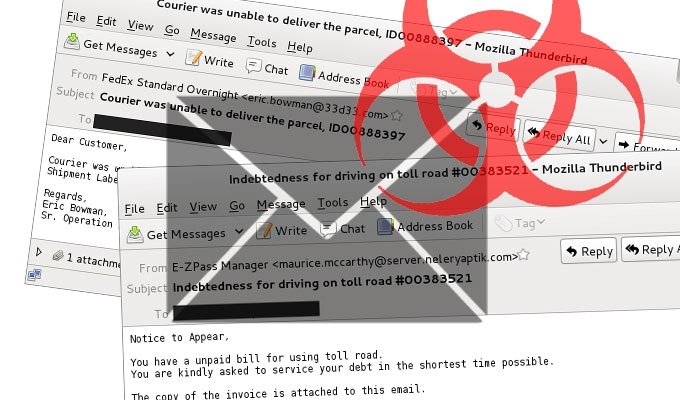
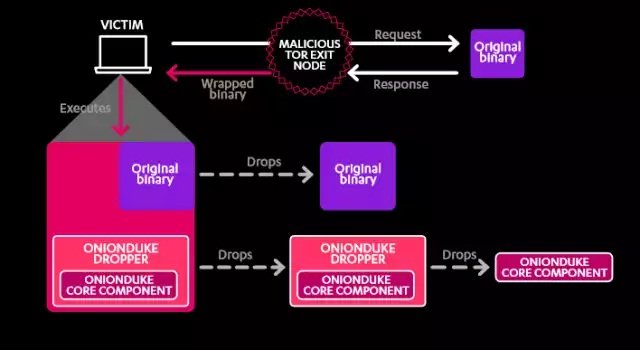
15-day-old campaign has spiked in past 48 hours, with >5,000 new infections daily. Attackers have hijacked thousands of websites running the WordPress content management system and are using them toRead More →