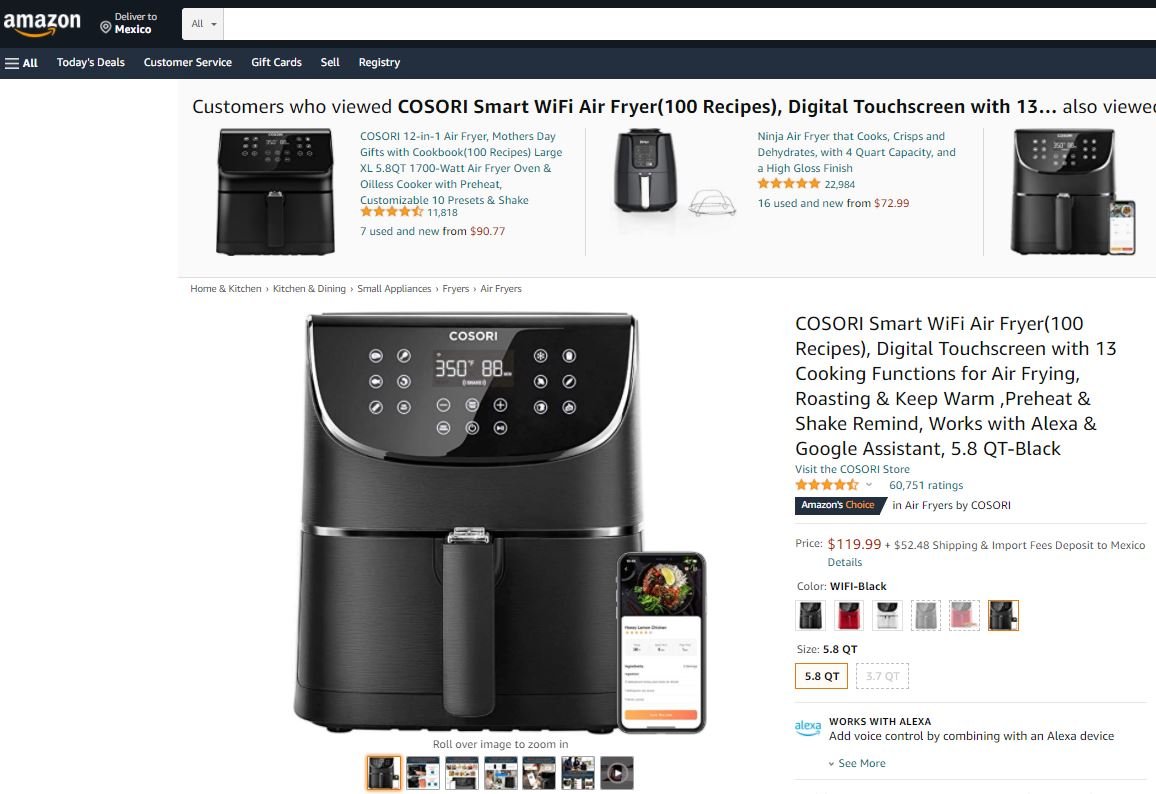
Cybersecurity specialists reported the detection of at least two critical vulnerabilities in the COSORI SMART WIFI air fryer, an Internet-enabled air fryer that is popular with Amazon. Users of the COSORI Smart WiFi air fryer can control the device through a smartphone app, taking full control of the functions of this new utensil.
This air fryer is also enabled for compatibility with Alexa and Google Assistant, so some voice commands are enough to keep track of what you’re cooking.
According to the report, successful exploitation of these flaws would allow threat actors to exploit arbitrary code on vulnerable devices. Below are brief descriptions of reported flaws, in addition to their security keys and scores assigned by the Common Vulnerability Scoring System (CVSS).
CVE-2020-28592: A boundary error in configuration server functionality would allow remote attackers to use a specially designed JSON object, cause memory corruption, and execute arbitrary code on the target system.
The vulnerability received a score of 7.4/10 and its successful exploitation would allow remote attackers to execute arbitrary code relatively easily.
CVE-2020-28593: Threat actors can abuse backdoor functionality in the software within the configuration server functionality. This functionality can be exploited to fully access the application that controls this device, committing the affected system.
This flaw received a CVSS score of 7.4/10, so it is considered a critical vulnerability.
Flaws reside in the following 5.8-quarter Cosori Smart versions CS158-AF: 1.1.0.
While flaws can be exploited by remotely unauthenticated threat actors, cybersecurity experts have not reported malware associated with the attack or attempted active exploitation.
For now, no security patches have been released to mitigate the risk of exploitation, although manufacturers are expected to address flaws in the next application update. To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











