TP-Link has released a fix for a severe vulnerability in its Archer AX21 router. This vulnerability might have allowed attackers to take control of the device and carry out arbitrary operations.

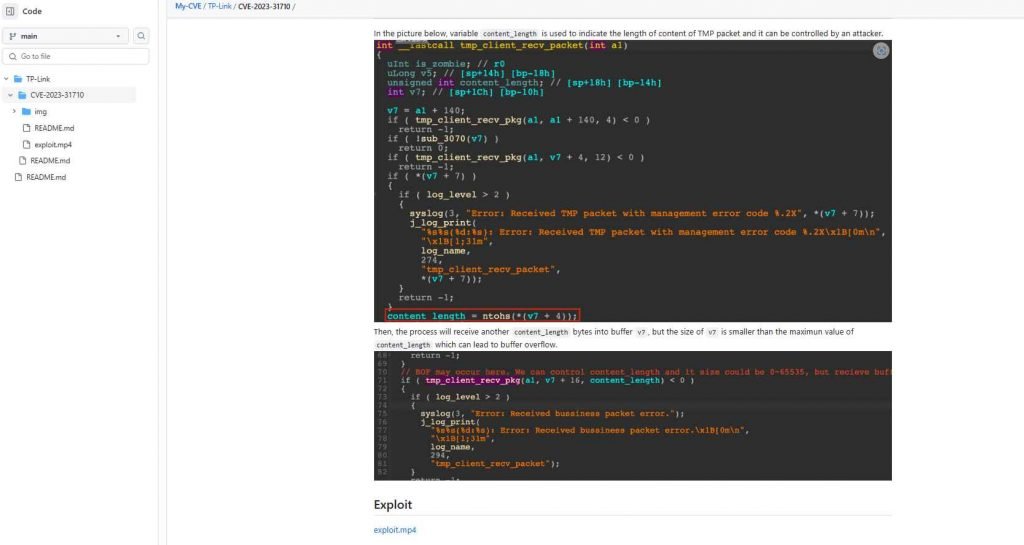
This vulnerability, which has been assigned the identifier CVE-2023-31710, was discovered after a heap-based buffer overflow bug was discovered in the TP-Link Archer AX21 router’s /usr/lib/libtmpv2.so component. Xiaobye, an adept security researcher, is the one who discovered this security weakness and exposed it in full, which made it possible for TP-Link to quickly devise a solution to the problem. The absence of input sanitization in relation to the variable content_length is at the heart of the problem that we are now facing. A clever adversary might potentially alter this variable, which provides information on the length of the data included in the TMP packet. This vulnerability may be exploited by a hacker by submitting a request to the router that was painstakingly designed, which would then cause the router to carry out the commands. Archer routers only allow ‘admin’ users, who are endowed with full root access. This exacerbates the severity of the problem. Therefore, in the event that a threat actor is successful in getting command execution, that actor would therefore take control of the router and acquire administrative capabilities.
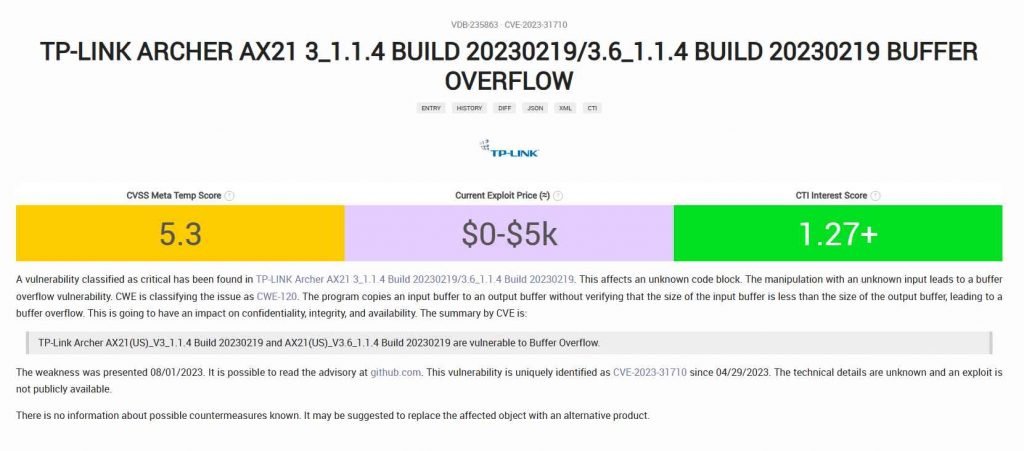
This security flaw affects particular router versions, including Archer AX21(US)_V3_1.1.4 Build 20230219 and Archer AX21(US)_V3.6_1.1.4 Build 20230219, among others. Nevertheless, TP-Link has released patches for these versions, which may be found under the names Archer AX21(US)_V3.6_230621 and Archer AX21(US)_V3_230621, respectively. It is recommended that consumers who are affected get their routers up to date as soon as they can.
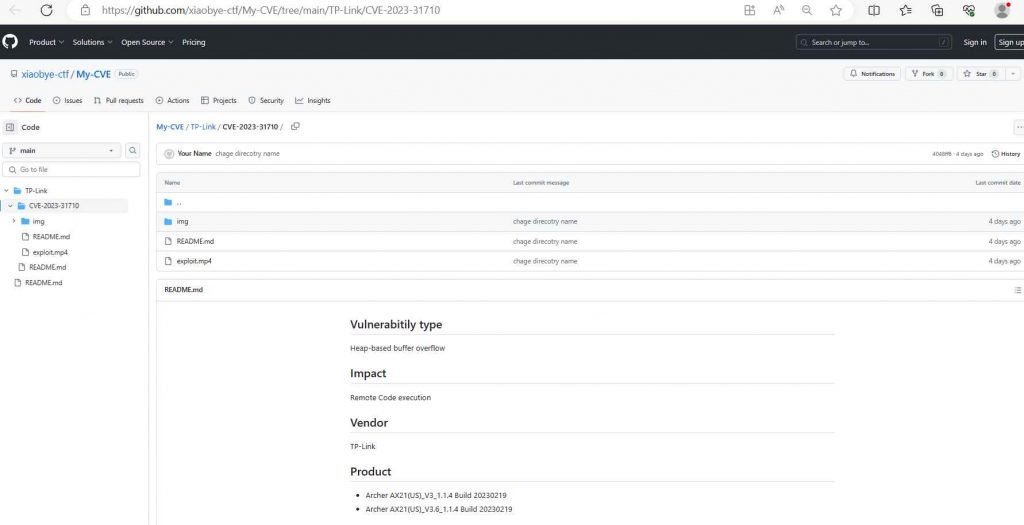
Xiaobye has continued his commendable efforts to shed light on this matter by publishing a compelling video presentation of exploiting the CVE-2023-31710 vulnerability on his Github repository.
In order to strengthen the safety of your router, you should take additional precautions in addition to updating the firmware on it.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











