A new privilege escalation vulnerability has been identified in the Linux kernel by researcher Davide Ornaghi. This vulnerability might enable a local attacker to execute code on vulnerable computers with elevated rights if the kernel is installed on those systems. Additionally, Davide published the proof-of-concept and the write-up. The vulnerability, which has been assigned the tracking number CVE-2023-0179, is a stack-based buffer overflow that exists in the Netfilter subsystem. An authorized attacker might exploit this issue to get elevated privileges as root if the attacker executed a program that had been carefully written for the purpose.
The Linux kernel has a framework known as netfilter that enables a variety of networking-related actions to be performed in the form of individualized handlers. This may be accomplished by filtering incoming network packets. Netfilter provides the functionality necessary for directing packets through a network and preventing packets from reaching sensitive locations within a network by offering a variety of functions and operations for packet filtering, network address translation, and port translation. [1] These features allow Netfilter to provide the functionality required for directing packets through a network.
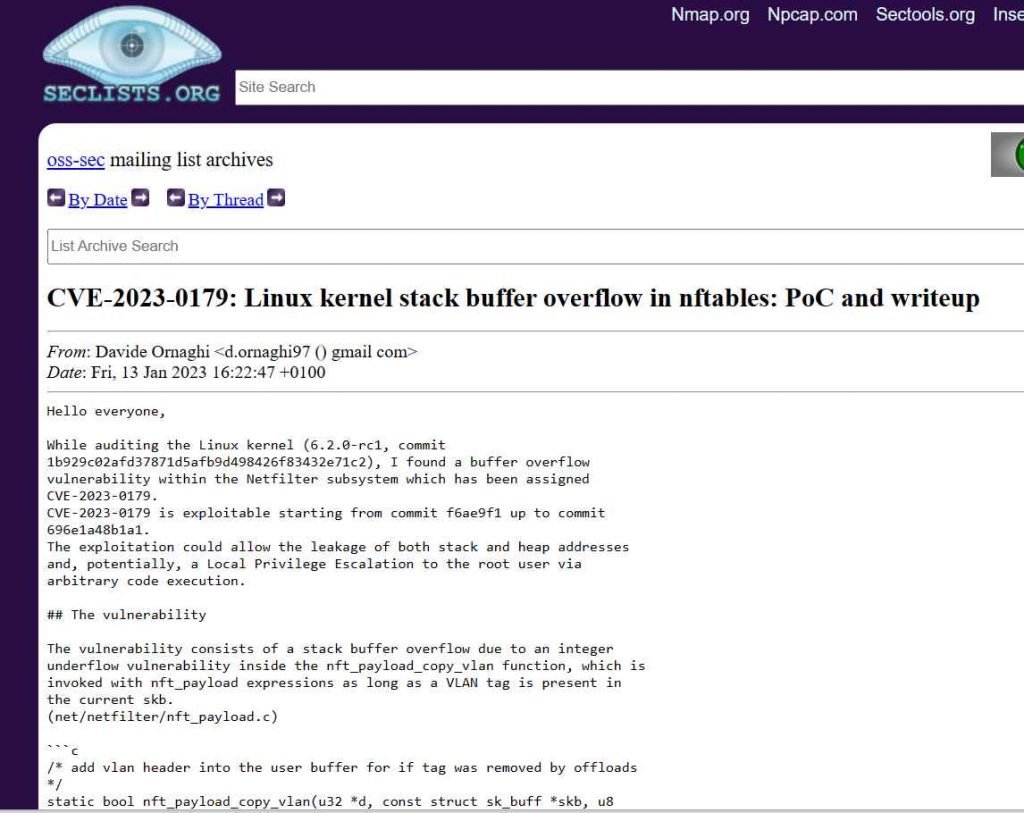
“The vulnerability consists of a stack buffer overflow caused by an integer underflow vulnerability within the nft payload copy vlan function,” which is triggered with nft payload expressions “as long as a VLAN tag is present in the current skb,” according to the description of the flaw.
Linux kernel 6.2.0-rc1 is vulnerable to the CVE-2023-0179 flaw. The vulnerability might be exploited to cause the disclosure of both the stack and heap addresses, as well as the possibility of a Local Privilege Escalation to the root user through the execution of arbitrary code. Users are strongly encouraged to upgrade their Linux servers as soon as possible and to apply fixes to distributions as soon as they become available. It is also advised that they only let trustworthy people access local systems and that they constantly check the systems that have been compromised.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











