Tails, well-known Linux distribution, has asked its users not to use the Tor Browser included with the operating system after detecting a critical prototype contamination vulnerability. Tor Browser is an open-source modification of Firefox, focusing on users’ privacy.
Tracked as CVE-2022-1802, the vulnerability would allow threat actors to corrupt the methods of an array object in JavaScript through prototype contamination, leading to the execution of malicious code in the context of a privileged process.
Another flaw tracked as CVE-2022-1529 could allow malicious hackers to send messages to the primary process to index a JavaScript object twice, leading to prototype contamination and JavaScript code execution.
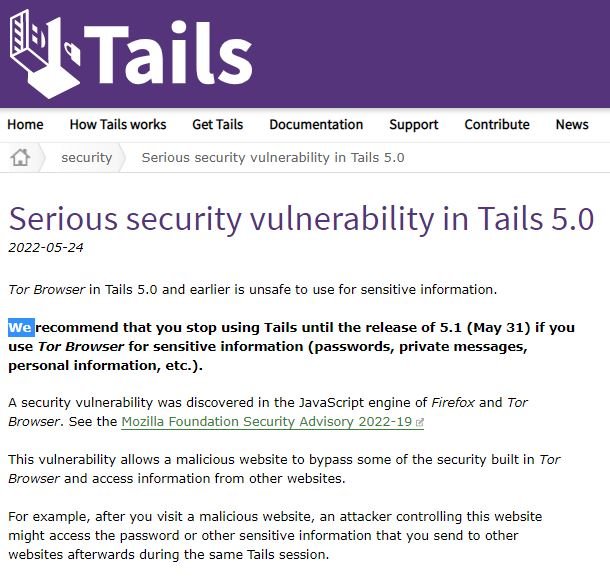
The developers of Tails have asked users not to start this browser while working with confidential information. The successful exploitation of the flaw would allow bypassing the security mechanisms in the distribution, leaving potentially critical information exposed.
“The vulnerability allows a malicious website to bypass some of the security built into Tor Browser and access information from other websites. For example, after visiting a malicious website, an attacker could access passwords and other sensitive records sent to other websites during the same Tails session,” the report said.
Tails added that this flaw does not break the anonymity and encryption of Tor connections, which means that it remains safe to access websites from Tails as long as the user does not enter sensitive information. Other applications in the operating system are not affected, as JavaScript execution is disabled.
There are no patches available, although the developers have already confirmed the release of the corrected version, Tails 5.1, scheduled for May 31. Meanwhile, the Tails community will be able to use the browser-independent version on Windows, Linux, and macOS systems.
Feel free to access the International Institute of Cyber Security (IICS) websites to learn more about information security risks, malware variants, vulnerabilities, and information technologies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











