Cybersecurity specialists report the detection of a dangerous “zero-click” vulnerability in a popular security camera model whose exploitation would allow threat actors to gain full access to an affected device and even to the home networks of millions of homes.
Tracked as CVE-2021-36260, the vulnerability was described as a remote code execution bug residing in some Internet of Things (IoT) cameras produced by Chinese company Hikvision. The researcher in charge of the report, known as “Watchful IP”, mentions that the exploitation would allow hackers to take full control of the device.
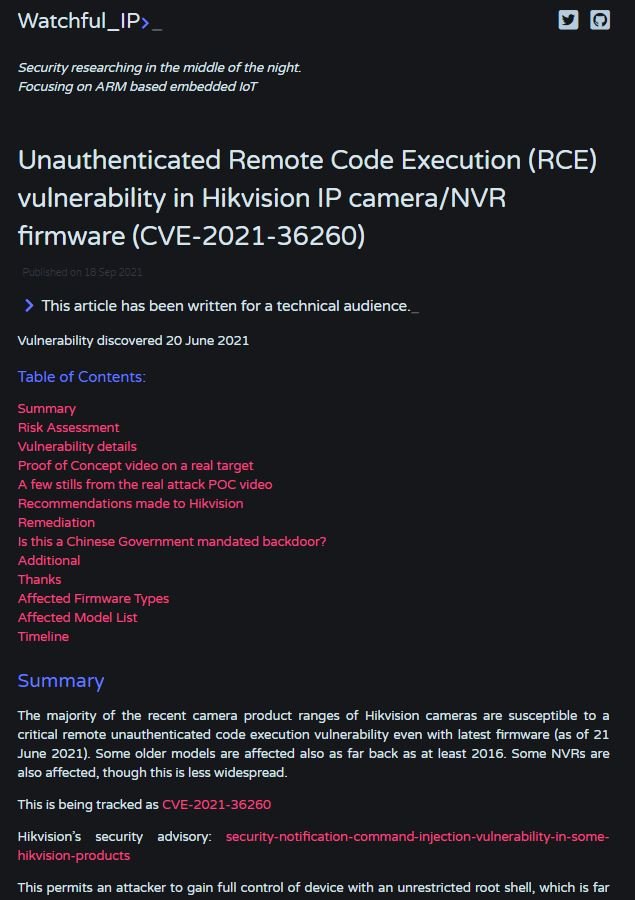
The vulnerability received a score of 9.8/10 according to the Common Vulnerability Scoring System (CVSS) and allows hackers to evade the protected shell, which restricts the use of this class of devices by owners for security reasons allowing a limited set of commands.
As some users may recall, zero-click vulnerabilities are considered especially critical because their exploitation does not require any interaction from affected users and usually leads to scenarios of total compromise of the target system.
On the other hand, many of the vulnerable devices could be installed on critical infrastructure, which could put sensitive operations and sensitive information at risk. To make matters worse, Watchful IP assures that this flaw has been present in affected products since at least 2016, so it is impossible to determine whether the error was exploited at some point.
Shortly after receiving the report, Hikvision acknowledged the existence of the flaw and issued a patch to correct it. The company also issued a security alert to disclose all affected products, mentioning that threat actors could take advantage of insufficient input validation to launch a malicious command injection attack.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











