A recent research indicates that it is possible to make solid-state drives (SSD) invulnerable to ransomware attacks by detecting infections and reversing encryption in microseconds and with consequences barely perceptible to the user. This research was developed by experts from the United Kingdom, the United States and South Korea.
“We know that most users don’t have anti-ransomware software, so we thought it would be good to protect them by developing an SSD with intrinsic ransomware features,” says DaeHun Nyang, one of the researchers in this project.
This project, dubbed SSD-Insider++ is based on relatively simple concepts, such as the search for activity patterns corresponding to a ransomware infection and its immediate interruption. Instead of doing this with antivirus tools, this process is performed by the SSD drive itself through a process run on the hardware driver.
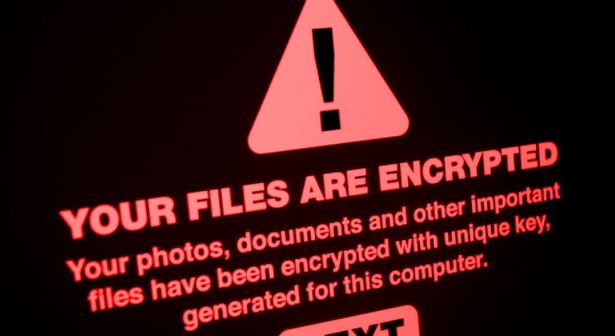
According to Nyang, when SSD-Insider++ detects ransomware activity, “the entry and exit to the storage is suspended, which allows the infection process to be cut short.”
Fundamentally, SSD-Insider++ isn’t just about detecting ransomware: as the developers also claim that it’s possible to reverse any resulting damage to compromised data in a matter of seconds. “Instead, this SSD takes advantage of the operational features of the hardware, retaining older versions of the data to hide the out-of-place upgrade nature of NAND flash memory. This allows you to back up original files without additional copies and instantly revert infected files.”
As a result of these tests, a system capable of detecting 100% of ransomware attacks and reversing encryption in less than 10 seconds was obtained, at the cost of only a 12% increase in system latency.
The findings of this group of researchers have already caught the attention of multiple technology manufacturers, although their implementation in the market is not a scenario that is just around the corner: “We have approached several companies in Korea, but we have not yet found any manufacturer that applies this technology; manufacturers are very conservative when it comes to adopting new technologies, especially if they can cause even a slight degradation of the performance of their products,” concludes Nyang.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











