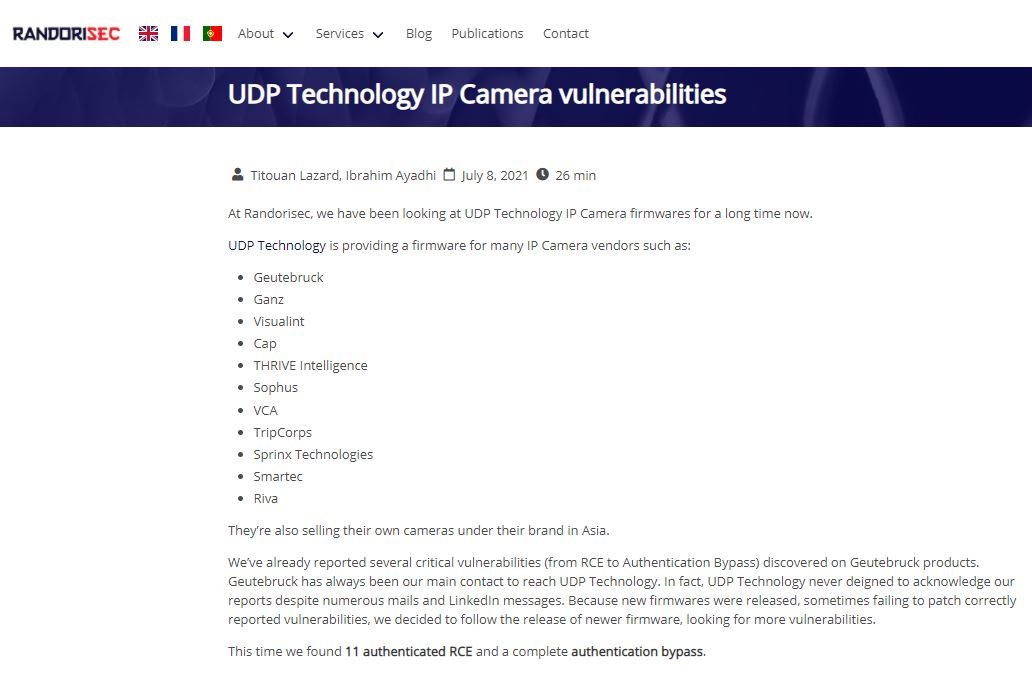
A recent cybersecurity report reports the detection of multiple critical vulnerabilities in the firmware of IP cameras with UDP Technology. UDP firmware is included in the cameras of a wide variety of manufacturers, including Geutebrück, VCA and Sprinx Technologies, among others.
Experts at Randorisec, the security firm in charge of the report, mention that some flaws in this firmware had previously been detected, including authentication errors and remote code execution flaws. In this new analysis, the experts confirmed the finding of 11 other remote code execution (RCE) flaws and an authentication error that makes it easier to exploit RCE flaws.
The researchers offered a detailed explanation of the finding of these flaws, adding that an in-depth analysis of the first flaws detected allowed them to detect authentication evasion failures and create proof of concept (PoC) exploits for RCE errors.
The vulnerabilities were reported to manufacturers last February and fully addressed with the release of a firmware update a couple of weeks ago. The list of flaws ranges from CVE-2021-33543 to CVE-2021-33554.
Davy Douhine, specialist in charge of the investigation, reports that the exploitation of any of these flaws would allow the deployment of other types of attacks: “During the tests, a combination of the flaw in the authentication process and an RCE vulnerability allowed us to gain root access; threat actors could interrupt the video transmission of the cameras, change their settings and even turn them off arbitrarily.”
The good news is that there are no known cases of active exploitation, although users of potentially affected devices are encouraged to upgrade to the latest UDP firmware version as soon as possible.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











