VMware security teams announced the release of some security patches to fix a severe flaw in vRealize Operations whose exploit would allow threat actors to steal administrator credentials on vulnerable servers. It should be remembered that vRealize Operations is an IT operations management platform, powered by artificial intelligence for private, hybrid, and cloud environments.
The flaw was discovered and reported to VMware by Positive Technologies web security researcher Egor Dimitrenko.
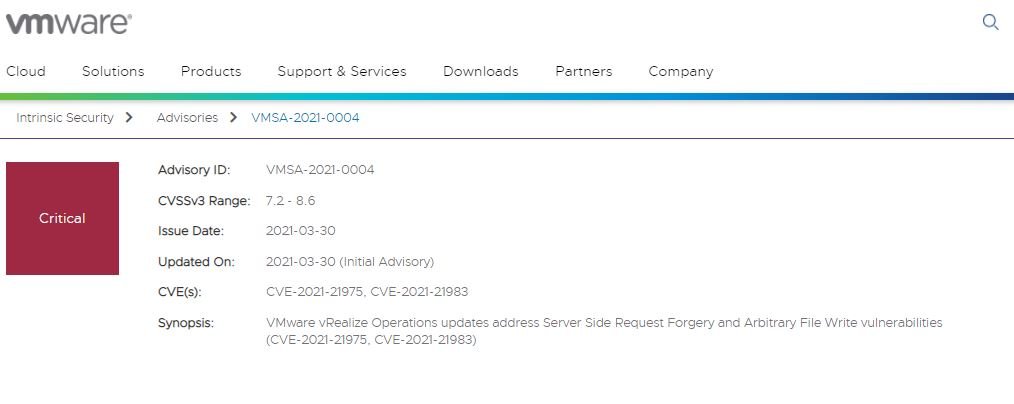
Treacked as CVE-2021-21975, this flaw exists due to a server-side request forgery (SSRF) error in the vRealize Operations Manager API. Threat actors could exploit this flaw remotely without interacting with affected user and without requiring authentication on the vulnerable system.
After receiving the report, VMware gave this flaw an 8.6/10 score based on the Common Vulnerability Scoring System (CVSS) scale; the company issued an additional report on the reported failures to add more details about the finding.
The company also released some instructions so that administrators who do not want to install updates at this time will deploy a workaround. VMware ensures that there is no impact after you apply mitigation measures, so the capabilities of the solution will not be affected.
According to the report, troubleshooting this issue requires deleting a configuration line from the home-security-context.xml file, in addition to restarting the CaSA service on the affected system. Complete information about this vulnerability and its mitigation methods are available on the company’s official platforms. In addition to this report, VMware announced the fix for CVE-2021-21974, a severe failure in the vRealize Operations Manager API that would allow threat actors to write files to arbitrary locations on the underlying operating system.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











