Critical infrastructure, media, and scientists targeted by suspected nation-state.
Researchers have uncovered an advanced malware-based operation that siphoned more than 600 gigabytes from about 70 targets in a broad range of industries, including critical infrastructure, news media, and scientific research.
The operation uses malware to capture audio recordings of conversations, screen shots, documents, and passwords, according to a blog post published last week by security firm CyberX. Targets are initially infected using malicious Microsoft Word documents sent in phishing e-mails. Once compromised, infected machines upload the pilfered audio and data to Dropbox, where it’s retrieved by the attackers. The researchers have dubbed the campaign Operation BugDrop because of its use of PC microphones to bug targets and send the audio and other data to Dropbox.
“Operation BugDrop is a well-organized operation that employs sophisticated malware and appears to be backed by an organization with substantial resources,” the CyberX researchers wrote. “In particular, the operation requires a massive back-end infrastructure to store, decrypt, and analyze several GB per day of unstructured data that is being captured from its targets. A large team of human analysts is also required to manually sort through captured data and process it manually and/or with Big Data-like analytics.”
Examples of targets infected in the campaign include:
- A company that designs remote monitoring systems for oil and gas pipelines
- An international organization that monitors human rights, counter-terrorism, and computer attacks on Ukrainian critical infrastructure
- An engineering company that designs electrical substations, gas distribution pipelines, and water supply plants
- A scientific research institute
- Editors of Ukrainian newspapers
Some examples of the way Operation BugDrop is more sophisticated include:
- Dropbox for data exfiltration. Organizations typically don’t prevent end users from accessing Dropbox and often don’t monitor connections. That helped the surveillance operation to remain stealthy.
- Reflective DLL Injection, a malware injection technique that was also employed by the BlackEnergy malware used in the Ukrainian power grid attacks and by Duqu in the Stuxnet attacks on Iranian nuclear facilities. Reflective DLL Injection loads malicious code without calling the normal Windows API.
- Encrypted DLLs that avoid detection by common anti-virus and sandboxing systems.
- The use of legitimate free Web hosting sites for command-and-control infrastructure. The hosting sites required little or no registration information, making it hard for researchers to learn much about the attackers.
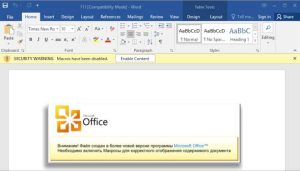
To become infected, targets had to open the malicious Word document attached to the phishing e-mail and enable macros. To increase the chance targets would change this default setting, the Word document included a graphic that looked like an official Microsoft notification. It read: “Attention! The file was created in a newer version of Microsoft Office programs. You must enable macros to correctly display the contents of a document.”
CyberX researchers stopped short of identifying a specific country involved but said Operation BugDrop was almost surely the work of a government with nearly limitless resources.
“Skilled hackers with substantial financial resources carried out Operation BugDrop,” they wrote. “Given the amount of data analysis that needed to be done on [a] daily basis, we believe BugDrop was heavily staffed. Given the sophistication of the code and how well the operation was executed, we have concluded that those carrying it out have previous field experience.”
Source:https://arstechnica.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











