The FireEye researcher Genwei Jiang revealed the exploit chain related to phishing attacks leveraging CVE-2016-4117 flaw recently fixed by Adobe.
Security experts at FireEye have recently spotted an attack leveraging on an Adobe zero-day vulnerability (CVE-2016-4117) recently patched.
The CVE-2016-4117 flaw affects older versions of the Adobe Flash, a few days ago the company was informed of a new zero-day vulnerability in the Flash Player software that was being exploited in cyber attacks in the wild. The company announced the fix for the CVE-2016-4117 on May 12 and confirmed that it affected Windows, Mac OS X, Linux and Chrome OS.
Adobe rated as critical the vulnerability, the issue was discovered by the security expert Genwei Jiang from FireEye, which also confirmed that it is being used in targeted attacks.
“A critical vulnerability (CVE-2016-4117) exists in Adobe Flash Player 21.0.0.226 and earlier versions for Windows, Macintosh, Linux, and Chrome OS. Successful exploitation could cause a crash and potentially allow an attacker to take control of the affected system.” reads the advisory published by Adobe.
“Adobe is aware of a report that an exploit for CVE-2016-4117 exists in the wild. Adobe will address this vulnerability in our monthly security update, which will be available as early as May 12. For the latest information, users may monitor the Adobe Product Security Incident Response Team blog.”
After the flaw was fixed, Genwei Jiang revealed the details of the previously undisclosed phishing attacks he reported to Adobe.
The experts explained that threat actors used phishing links and files to compromise Windows systems running Flash, and Microsoft Office.
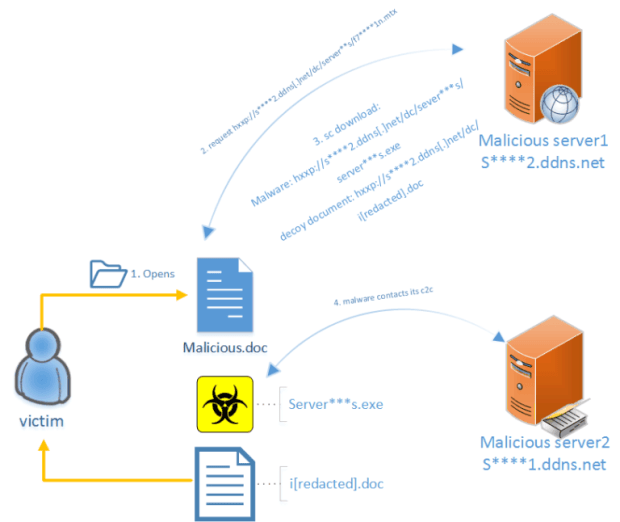
The expert explained that threat actors embedded the Flash exploit inside a Microsoft Office document, which they then hosted on a web server they controlled. They used a Dynamic DNS (DDNS) domain to reference the document and the malicious payload.
When victims open the malicious document, then the exploit downloads and executes the payload hosted on the crooks’ server. In order to avoid suspicion and make the attack stealth, threat actors then display victims a decoy document.
“On May 8, 2016, FireEye detected an attack exploiting a previously unknown vulnerability in Adobe Flash Player (CVE-2016-4117) and reported the issue to the Adobe Product Security Incident Response Team (PSIRT). Adobe released a patch for the vulnerability inAPSB16-15 just four days later.” reads a blog post published by FireEye.
“Attackers had embedded the Flash exploit inside a Microsoft Office document, which they then hosted on their web server, and used a Dynamic DNS (DDNS) domain to reference the document and payload. With this configuration, the attackers could disseminate their exploit via URL or email attachment. Although this vulnerability resides within Adobe Flash Player, threat actors designed this particular attack for a target running Windows and Microsoft Office.”
The post published by FireEye details the attack that proceeds as follows:
- The victim opens the malicious Office document.
- The Office document renders an embedded Flash file.
- If the Flash Player version is older than 21.0.0.196, the attack aborts.
- Otherwise, the attack runs the encoded Flash exploit.
- The Office document renders an embedded Flash file.
- The exploit runs embedded native shellcode.
- The shellcode downloads and executes a second shellcode from the attacker’s server.
- The second shellcode:
- Downloads and executes malware.
- Downloads and displays a decoy document.
- The malware connects to a second server for command and control (C2) and waits for further instructions.

Experts are warning about a possible spike in the attacks exploiting this flaw that was recently fixed.
Users should install the latest Adobe patch as soon as possible and FireEye suggests them to employ additional mitigations, such as Microsoft EMET to prevent exploit attacks.
Source:https://securityaffairs.co/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.