A new archive containing alleged voting records of millions of US citizens is available on a hidden service on the dark web.
Joseph Fox from Motherboard discovered alleged voting records of millions of American citizens on a website in the dark web. The data were published on a website linked to a notorious cybercrime forum, The Hell. The archive is hosted on a password-protected hidden service, which was referred by the administrator of The Hell.
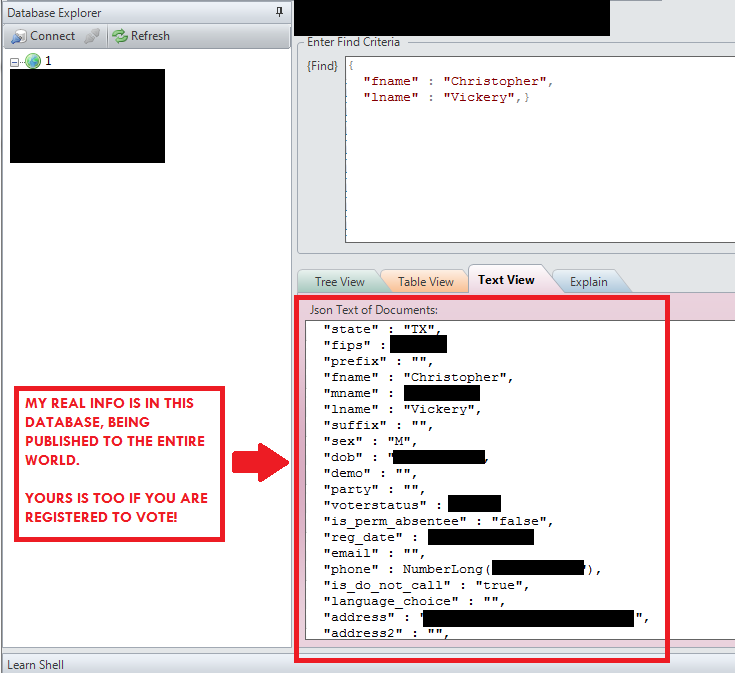
The archive contains voters’ information, including full names, dates of birth, the date they registered to vote, addresses, voting records from previous elections and political affiliations. The origin of the voting records is still a mystery.
“The two largest files are 1.2 GB and 1 GB, respectively, and each contain at least a million entries. The folder containing the files is called “US_Voter_DB,” though Motherboard could not independently verify the contents’ legitimacy.”Fox wrote .
This isn’t the first time that such kind of information is discovered on the web. In December 2014, the security expert Chris Vickery has discovered a misconfigured archive exposes the personal details of 191 million U.S. voters. The records include voters’ full names, unique voter IDs, unique voter IDs, date of births and phone numbers. A few days later, another archive was discovered online containing voting records, it was a misconfigured database discovered by Chris Vickery containing data of US voters, including 19 million profiles with private information on religion, gun ownership and more.
The archive recently discovered does not contain social security numbers, neither sensitive data or financial information, but it could have an enormous s value for a hacker that desire to take advantage of the next US election to run phishing attacks.
In my post on “2016 Cyber Security Predictions: From Extortion to Nation-state Attacks,” I wrote about the possible exploitation of the US elections for new hacking campaigns launched by nation-state-actorsand cybercriminals.
“Social media are a primary communication method for politicians, the online activity will be intense in the period before the elections and cyber criminals and nation-state actors will try to exploit the event to launch cyber-attacks.
Hackers will exploit the event to spread malware and infect computers of a large number of people. Expect lures made to look like political party or candidate email, explaining their program or advocating an online petition or survey on election issues.
There is also the risk that state-sponsored hackers will run spear phishing attacks and watering hole attacks in order to compromise machines of specific individuals or groups.”
Source:https://securityaffairs.co/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











